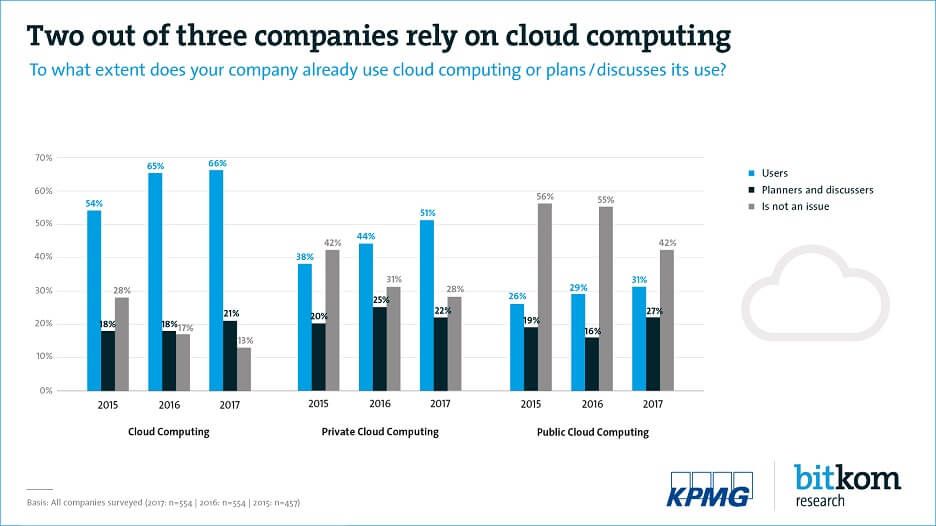
Confidentiality, availability, integrity – these are three of the most important attributes of an IT security concept. In order to meet these requirements in the best possible way, some companies prefer on-premises resources or the private cloud. But they often do it for the wrong reasons: According to the Bitkom Cloud Monitor 2018, 63 percent of the companies surveyed fear "unauthorized access to sensitive company data" and 56 percent even fear "loss of data" if they use the public cloud. However, on-premises IT systems are not fundamentally more secure. Often the opposite is true. Hardly any other company can offer the same level of up-to-dateness, manpower, technology and availability as a highly specialized public cloud provider.
IT security: Public cloud versus on-premises
Cloud providers, for example, employ teams of experts who take care of the operation, maintenance and servicing of hardware and software around the clock. For example, with images that form the basis of installed operating systems: An extensive operating team always keeps an eye on images, reacts immediately if errors or security incidents become known in common operating systems and immediately implements patches from the operating system provider. If necessary, cloud providers also develop their own solutions to resolve incidents promptly if the operating system provider's solution takes too long. Cloud users are often the first to benefit from updates that increase security.
In addition to the question of architecture, IT managers are also concerned about the necessary security knowledge: Sophisticated security mechanisms are ineffective if only a few experts understand them or if they are not able to implement them completely. Yet it can be difficult and expensive to hire these particular specialists. For this reason, usability and user experience also play an important role when it comes to IT security. The message to CIOs is therefore that security functions must be simple, convenient and reliable to implement. This is the only way to ensure that IT services in companies achieve a high level of security.
But is cloud computing really always the better choice when it comes to IT security? That depends on the provider and how it implements security tasks. Take confidentiality, for example: encrypting and storing data is basically a very simple task. But strong encryption is not enough in itself. It depends on how the keys themselves are handled. After all, they must also be stored in a secure procedure. That's why the Open Telekom Cloud has its own service for this purpose, the Key Management Service (KMS). The corresponding codes for decryption are stored there in a particularly secure manner in special hardware modules, so-called Hardware Security Modules (HSM) – something that is not a matter of course in the Infrastructure-as-a-Service (IaaS) environment.
The use of open source systems such as OpenStack in the business world is still relatively rare, although it is on the rise. The open source code is continuously developed and controlled by a large community; from the network functions to the hypervisor to specific storage formats. This provides a level of transparency that proprietary software vendors cannot provide. In the case of the latter, the development and structure can only be viewed by the provider himself. Anyone using such IaaS offerings has to have confidence in its functionality, integrity and timeliness, but cannot control this.
Provider selection is therefore crucial, but not only because of the underlying software architecture. It's also about the brand itself, which can sometimes be used to determine which legal regulations a provider is obliged to comply with. Here, European providers differ fundamentally from US providers. One thing is clear: every company that offers IT resources in Germany must comply with German laws. However, a US company is also subject to US regulations. For example, the CLOUD Act: According to this law, US companies must grant the US authorities access to personal data as required in the course of investigations – regardless of where it is stored! According to many experts, the US CLOUD Act and the EU GDPR are mutually exclusive.
Companies such as Telekom, which has its headquarters in Germany and operates the data centers for their public cloud services at the same location, are not subject to these regulations, but act exclusively in accordance with the EU’s GDPR. In addition, the Open Telekom Cloud’s data centers have already been certified several times by independent bodies for their high level of data security and data protection. These include the ISO 27001 certificate based on the so called IT-Grundschutz catalogue.
However, the location advantage is only one aspect. The Open Telekom Cloud also provides many mechanisms that enable customers to implement secure solutions with great convenience and little effort. One example is security groups, also known as firewall rules. The principle of these security groups is familiar to most network administrators. Nevertheless, they are usually difficult to configure. The Open Telekom Cloud is changing this. This is because security groups can be automated to a high degree. Companies can, for example, directly tell an application how to behave. Previously a highly complex process, companies can now do this with just a few clicks or a configuration management recipe. In addition, the Open Telekom Cloud’s security groups can be addressed directly via programmable interfaces (APIs), the console or command lines.
So-called distributed denial-of-service (DDoS) attacks are a serious threat to IT infrastructures. The Open Telekom Cloud also offers special protection against these attacks: the Anti-DDoS service. Without such a service and the backing of a provider associated with it, companies are generally exposed to such attacks without any chance of defending themselves. This is because it is always a test of strength that at a certain level only a provider like Telekom can attain, due to the fact that it has a global infrastructure that is larger than that of any attacker. This means that DDoS attacks on services hosted in the Open Telekom Cloud can be reliably fended off.
IT security is one of the greatest challenges facing companies. It's understandable that many people are hesitant about the idea of a shared infrastructure, because that’s exactly what a public cloud is. This fear can, however, be overcome by the facts: If one takes a closer look at this topic, one will realize that a public cloud infrastructure with the right conditions can even offer a significantly higher degree of IT security than self-managed resources. However, this requires appropriate expertise. Or the advice of experts – such as Telekom's cloud team.
Author Nils Magnus is an expert on complex issues surrounding the cloud, security, networks and compliance. He has been working as cloud architect for the Open Telekom Cloud at T-Systems since 2017. Nils Magnus is 48 years old and lives in Berlin.